Your AI Agents Are Over-Privileged. Here's the Data.
Over-privileged AI agents drive 4.5x more security incidents. New research from Teleport, Gravitee, and Help Net Security shows why access scope is the #1 predictor of AI security failures.
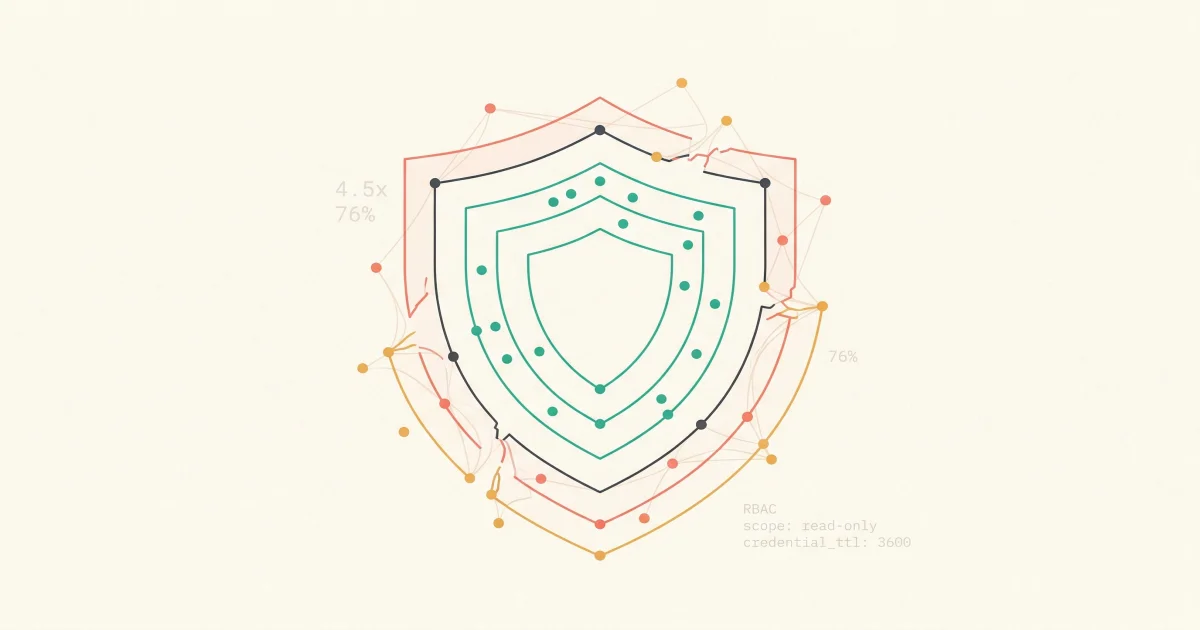
Teleport's 2026 report found that over-privileged AI systems experience 4.5x more security incidents. Here is what the data says, why it keeps happening, and the five-step fix every engineering leader should start this week.
Organizations giving AI systems excessive permissions experience 4.5 times more security incidents than those enforcing least privilege. That is the headline finding from Teleport's 2026 State of AI in Enterprise Infrastructure Security report, based on interviews with 205 CISOs and security architects at companies with 500 to 10,000+ employees.
The number that should concern every VP of Engineering: 76% incident rate for organizations with broad AI permissions versus 17% for those limiting AI to task-specific access. Access scope was more predictive than industry, maturity level, or stated confidence in AI security.
Key Takeaways
The Numbers Are Worse Than You Think
Teleport surveyed 205 security leaders in December 2025. The gap between AI adoption and AI governance is staggering.
| Metric | Number | Source |
|---|---|---|
| Organizations with AI in production | 92% | Teleport 2026 |
| Security leaders concerned about AI risk | 85% | Teleport 2026 |
| Experienced or suspect an AI-related incident | 59% | Teleport 2026 |
| Grant AI higher access than humans for same task | 70% | Teleport 2026 |
| Still use static credentials for AI systems | 67% | Teleport 2026 |
| Have no formal AI governance controls | 43% | Teleport 2026 |
| Have automated controls at machine speed | 3% | Teleport 2026 |
| Evaluating or deploying agentic AI | 79% | Teleport 2026 |
| Feel prepared for agentic AI security | 13% | Teleport 2026 |
| Have full visibility into agent permissions | 21% | Help Net Security 2026 |
That last row deserves its own sentence. 82% of executives believe their existing policies protect them from unauthorized agent actions. Only 21% can actually see what their agents access.
Why This Keeps Happening
The root cause is not that security teams are careless. It is that AI agents inherited the deployment patterns of the tools that came before them.
Service accounts on steroids
Most organizations treat AI agents as extensions of human users or generic service accounts. Only 21.9% of teams treat AI agents as independent, identity-bearing entities according to Gravitee's 2026 AI Agent Security Report. The agent gets the same broad credentials as the service it was bolted onto. Nobody scoped the access because nobody thought of the agent as a separate actor.
Speed beats governance
79% of organizations are already evaluating or deploying agentic AI. Only 13% feel highly prepared for the security implications. The deployment timeline is measured in weeks. The governance timeline is measured in quarters. AI agents ship before the security review happens.
Static credentials everywhere
67% of organizations still rely on static credentials for AI systems. Static credentials do not expire. They do not rotate. When an agent with static credentials gets compromised, the attacker has persistent access until someone notices. Teleport's data shows a 20% increase in incident rates correlating with static credential use.
No controls at machine speed
AI agents can make hundreds of infrastructure changes per minute. Only 3% of respondents have automated controls that operate at machine speed. 43% report that AI makes infrastructure changes without human oversight at least monthly. 7% have no idea how often autonomous changes happen. Manual review processes cannot keep up with agents that operate at machine speed.
The Confidence Paradox
Here is the most counterintuitive finding from the Teleport report. Organizations that report strong confidence in their AI security have an incident rate 2.2 times higher than those with low or neutral confidence.
This is not a contradiction. It is a selection effect. The most "mature" organizations are the ones deploying complex agentic workflows. They have more AI doing more things with more access. They feel confident because they have invested heavily in AI. But their security controls have not kept pace with the complexity they deployed.
Teleport CEO Ev Kontsevoy framed it clearly: "It's not the AI that's unsafe. It's the access we're giving it."
The lesson for engineering leaders: confidence in AI maturity is not the same as confidence in AI security. Audit your access controls before you audit your capabilities.
What Responsible AI Agent Access Looks Like
The fix is not complicated. It is the same principle that has governed infrastructure security for decades: least privilege. Applied to AI agents, it looks like this.
1. Treat every agent as a first-class identity
An AI agent is not an extension of the engineer who deployed it. It is an independent actor with its own identity, its own credentials, and its own audit trail. If your IAM system does not have a concept of "agent identity," you have a gap. Nancy Wang, CTO of 1Password, put it directly: "Baseline guardrails must be built into platforms themselves. Sandboxed tool execution, scoped credentials, runtime policy enforcement."
2. Scope access to the task, not the environment
If an agent investigates incidents, it needs read access to logs, metrics, and traces. It does not need write access to your database. It does not need permission to modify infrastructure. Every additional permission is additional blast radius.
Ask this question for every AI agent in your stack: what is the minimum set of permissions this agent needs to do its job? If you cannot answer that question, the agent is over-privileged.
3. Replace static credentials with short-lived tokens
Static credentials are the single most common mistake. Teleport's data correlates static credential use with measurably higher incident rates. Short-lived, scoped tokens limit the window of exposure. If a token is compromised, it expires before it is useful.
4. Log everything the agent does
You cannot secure what you cannot see. Only 24.4% of organizations have full visibility into agent-to-agent communication, according to Gravitee's 2026 report. Every action an AI agent takes should be logged, attributed, and auditable. When something goes wrong, you need to trace exactly what the agent did and why.
This is where transparent knowledge and evidence chains become a security requirement, not just a trust requirement. If you cannot see the reasoning behind an agent's actions, you cannot determine whether those actions were authorized.
5. Build approval workflows for destructive actions
Read operations are low risk. Write operations that change production state are high risk. Any AI agent that can modify infrastructure, restart services, or deploy code needs explicit human approval for destructive actions. No exceptions.
What to Do This Week
You do not need a six-month security initiative. Start with five things.
-
Inventory your AI agents. List every AI system that has access to production infrastructure. Include the unofficial ones. The average enterprise has an estimated 1,200 unofficial AI applications in use according to Help Net Security.
-
Audit their credentials. For each agent, document what it can access. If the answer is "everything the service account can access," that is a problem.
-
Check for static credentials. Any AI system running on long-lived API keys or service account passwords needs to be migrated to short-lived tokens.
-
Verify your logging. Can you trace every action an AI agent took in the last 24 hours? If not, you have a visibility gap that needs to close before you deploy more agents.
-
Define blast radius. For each agent, answer: if this agent is compromised or malfunctions, what is the worst it can do? If the answer scares you, reduce the permissions.
The Access Problem Is the Whole Problem
The Teleport report makes one thing clear. The organizations experiencing the most AI security incidents are not the ones deploying the most AI. They are the ones deploying AI with the most access. Over-privilege, not adoption, is the risk factor.
Every engineering leader deploying AI agents into production infrastructure needs to ask the same question they ask about any production system: what happens when this goes wrong, and how bad can it get? The answer depends entirely on how much access you gave it.
Frequently Asked Questions
How do I know if my AI agents are over-privileged?
Audit the credentials your AI systems use. If they share a service account with broad access, or if you cannot list exactly which resources the agent can touch, it is over-privileged. Teleport's 2026 research found that 70% of organizations grant AI higher access than a human would need for the same task.
What is the biggest security risk with AI agents in production?
Over-privileged access. Teleport's 2026 report found that access scope is the single strongest predictor of AI-related security incidents. Organizations with broad AI permissions had a 76% incident rate versus 17% for those enforcing least privilege.
Should I use static credentials or short-lived tokens for AI agents?
Short-lived, scoped tokens. Static credentials correlated with a 20% increase in incident rates according to Teleport's research. Treat AI agents like any other identity in your system and rotate credentials frequently.
How do I evaluate whether an AI agent vendor takes security seriously?
Ask three questions. What access does the agent require? Can you see and audit every action it takes? Does it support on-prem or VPC deployment? If the vendor cannot answer all three clearly, keep looking.
Do AI agents need the same access controls as human users?
Yes, and potentially stricter ones. AI agents operate at machine speed and can make hundreds of decisions per minute. Only 3% of organizations have automated controls governing AI behavior at machine speed. The blast radius of a misconfigured agent is larger than a misconfigured human.
See How TierZero Handles Access
TierZero Production Agents operate with scoped, auditable access. Every investigation shows a full evidence chain. Every action requires approval. Deploys on-prem for regulated industries. See what responsible AI agent access looks like in practice.
Co-Founder & CEO at TierZero AI
Previously Director of Engineering at Niantic. CTO of Mayhem.gg (acq. Niantic). Owned social infrastructure for 50M+ daily players. Tech Lead for Meta Business Manager.
LinkedIn

