AI for Cloud Security: How Continuous Reasoning Beats Periodic Scanning
AI for cloud security replaces periodic scanning with continuous reasoning across deploys, configuration drift, and runtime telemetry. How TierZero's Proactive Discovery agent finds exposures before they become incidents.

The riskiest cloud exposures aren't in the CVE feed. They're configuration drift, schema mismatches, and over-privileged services nobody knows about yet. AI cloud security agents reason continuously across infrastructure, deploys, and runtime telemetry to catch what static scanners miss.
Key Takeaways
- The riskiest cloud exposures aren't in the CVE feed. They're the configuration drift, schema mismatches, and over-privileged services nobody knows about yet.
- Static scanners run on a schedule and only catch known patterns. Continuous AI agents reason across infrastructure, deploys, and runtime telemetry to find what scanners miss.
- TierZero's Proactive Discovery agent runs all day, every day. When a CVE drops, it already knows which services in your environment are exposed and what the patch looks like.
Cloud security has a discovery problem.
The exposures that take companies down are almost never the ones in the CVE feed. They're the IAM role that picked up an extra permission six months ago and never got cleaned up. They're the deploy that quietly bumped a dependency past its supported version. They're the staging bucket that drifted public during a half-finished migration that the original owner left the company before finishing. By the time the weekly scan picks any of these up, an attacker already has.
The category watching for this kind of thing is forming fast, and most of it is unimpressive. Vendors are slapping "AI" on everything from CSPM dashboards to SAST tools, then stapling a chatbot on. Calling that cloud security AI in 2026 is a stretch.
So what does the term actually mean, what can an autonomous agent catch that a static tool can't, and what has to be true about the agent before you let it touch production. That's what the rest of this is about.
What "AI for Cloud Security" Actually Means in 2026
The category is messy because the underlying capability is genuinely new. It helps to separate the layers.
Static SAST and DAST tools scan code and running services for known vulnerability patterns. They're good at what they do: find the SQL injection, the unpatched library, the missing security header. But they only see the snapshot you point them at. The CSPM and posture management tools sit one layer above, checking your cloud configuration against a rule set. Is this S3 bucket public? Is this IAM role over-privileged compared to a benchmark? Useful, but it stops at "does this match a rule someone wrote down." Traditional vulnerability scanners are even further out: schedule scans, generate reports, dump the findings into a queue your security team has to manually triage. The scanner doesn't know which findings matter in your specific environment, which services are reachable from the internet, which ones touch customer data, or which ones are about to be deprecated next sprint.
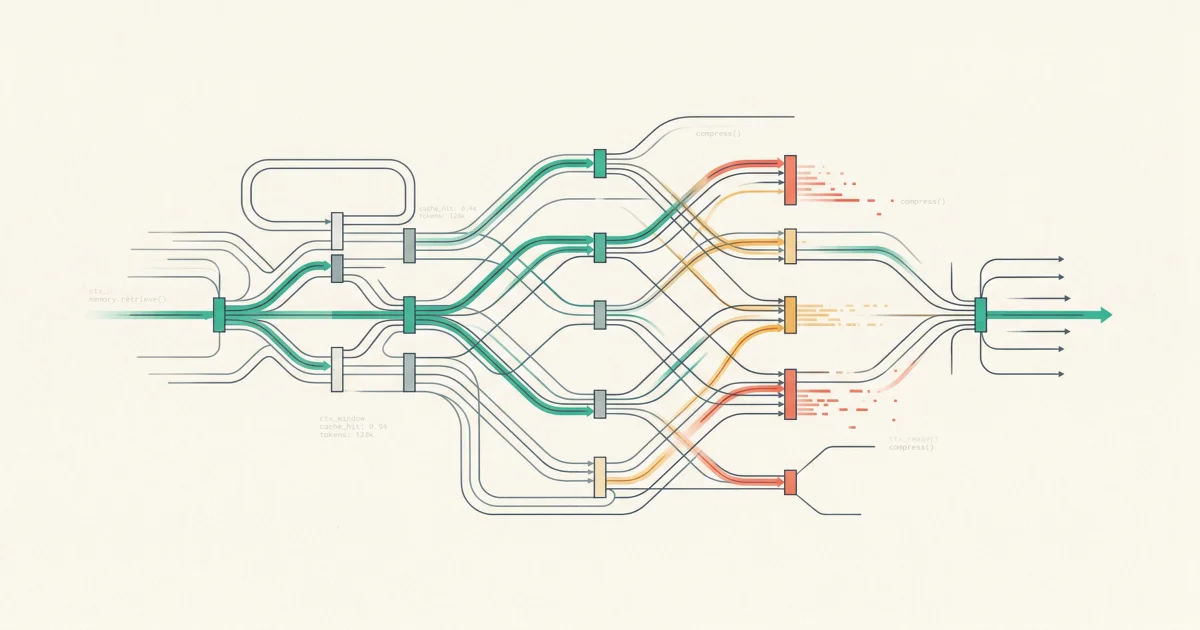
AI cloud security agents are a different shape of thing. They run continuously instead of in scheduled scans. They reason across whatever signals you give them access to: infrastructure state, deploy events, drift, runtime telemetry, recent code changes, alert patterns. They build context over time and remember it. And when something matters, they connect dots a human would have had to connect by hand, if a human had had time to look.
That shift, from periodic scanning to continuous reasoning, is what's worth paying attention to.
The Shift From Periodic Scanning to Continuous Reasoning
Static scanners assume the world holds still between scans. It doesn't. The average mid-market engineering org pushes hundreds of deploys a week, every one of which can touch IAM, network policy, dependency versions, runtime configuration. By the time the weekly compliance scan runs, the surface area looks nothing like it did when the rules were written.
The other problem is that scanners only catch what their rules describe, and the interesting risks are the ones nobody wrote a rule for. A perfectly safe change interacts with a perfectly safe configuration and creates something neither team owns. No rule fires. The drift sits there until somebody trips over it.
Continuous reasoning fixes both. Every deploy gets watched as it happens, alongside the runtime telemetry and the alert stream. When something looks off, the agent doesn't just fire a rule, it investigates: pulls change history, related services, historical patterns, decides whether this is signal or noise, surfaces it with context if it's signal. The same architecture that handles incident response (investigate, correlate, reason, recommend) applies cleanly to security. The agent doesn't care whether the trigger was a 3 AM page or a quietly shifting permissions boundary.
What an AI Cloud Security Agent Does Differently
TierZero's Proactive Discovery agent runs continuously and watches the relationships between services, not just the services themselves. Take a misconfigured IAM policy. In isolation, it might be benign. The same policy attached to a service that just started reading from a customer-data table is a different story. A scanner sees the policy. The agent sees the relationship.
It also tracks change as a pattern, not as a single event. Configuration drift isn't a state, it's a trajectory: the service whose permission set has been quietly expanding deploy by deploy, the capacity headroom shrinking week over week, the dependency chain forking away from the version your security team approved. None of these trip a single alert. They show up as a story that only emerges when somebody is keeping a long-running record.
Same idea applies when a CVE drops. Instead of handing you a list of every package in your repo, the agent correlates infrastructure state with deployment history, alert patterns, and recent code changes to figure out which services in your environment are actually affected and what remediation looks like. And it surfaces silent failure modes that don't trip your existing alerts because nobody wrote an alert for them: schema drift between a producer and consumer service, capacity headers technically green but trending toward yellow, dependency version mismatches that haven't caused an incident yet but will.
The Drata team running TierZero has seen this play out across their security and reliability stack. 42% MTTR reduction. Over 7,000 engineering hours saved per year. A meaningful share of those hours come from issues the agent surfaced before they paged anyone.
Three Categories of Risk Only Continuous AI Catches
Static tools catch static problems. Three categories of moving problem are where continuous agents earn their keep.
1. Configuration Drift
Drift is what happens between the moment your IaC was reviewed and the moment your auditor shows up. Roles pick up extra permissions during an emergency that nobody removed. Certificates expire on services nobody owns. Network policies grow IP exceptions that were supposed to be temporary. Storage buckets get public read flags during a migration that never finished.
A scanner catches drift only when a rule already describes the bad end-state. A continuous agent catches drift because it watched it happen. It saw the deploy, saw the manual change in the console, saw the role expansion, noticed the pattern was unusual for that service. The Proactive Discovery agent flags drift the moment it occurs, with the chain of custody for what changed, who changed it, and which services are now exposed.
2. Dependency Surprises
A CVE drops on a popular library. Your security team gets a Slack ping. What happens next?
The traditional answer: grep the lockfiles, ask the service owners, file tickets, hope you got everything before the exploit goes public. That costs hours per CVE on a good week. On a bad week it costs the whole afternoon and you still aren't sure you found everything.
When a CVE is published, the TierZero agent correlates infrastructure state, deployment history, alert patterns, and recent code changes to determine which services in the customer's environment are actually affected and what the patch path looks like. The output isn't a list of packages. It's: these three services are exposed, this is the version they're pinned to, this is the safe upgrade target, here's the rollout order based on dependency graph and historical deploy risk. Different output, different workflow.
3. Silent Failure Modes
These are the ones nobody alerts on because nobody knew they could happen. A producer service starts emitting a slightly different schema, the consumer keeps running, fields get dropped silently. A capacity metric stops trending up the way it used to. A retry budget that used to clear in seconds now takes minutes.
None of this trips a page or shows up in a vulnerability scan. All of it is the early warning sign of either a reliability incident or a security exposure, depending which way the failure cascades. A continuous agent watches gradients, not just thresholds. It notices when something is behaving differently from how it has behaved historically, and surfaces the deviation before anyone trips over it.
The Trust Ceiling
Continuous reasoning is the easy part. The hard part is what happens when the agent wants to act.
A purely advisory security AI (generates findings, files tickets, hands off to a human) is a more expensive scanner. The value compounds when the agent can actually take action: rotate the leaked credential, open the patch PR, quarantine the misconfigured service, roll back the deploy that introduced drift. But action raises the bar on trust. There's a ceiling on how much you can hand to an autonomous system before the risk-reward stops penciling, and that ceiling moves up or down based on what's true about the system.
Auditability is the first requirement. You need to see what the agent knows, where it learned it, and what it's doing with the information. TierZero's Memory Explorer surfaces exactly that: if the agent thinks a service is internet-facing, you click through and see the evidence chain (the deploy event, the IAM policy, the load balancer configuration). If it's wrong, you correct it once and the correction sticks. Approval workflows are the second requirement. Read-only investigation can run autonomously. Anything destructive (opening PRs, rotating credentials, modifying production configuration) sits behind a human approval until you've seen enough to relax that. The agent proposes with full context; the human approves. Over time low-risk actions can be auto-approved. High-risk ones never should be.
The other two requirements are more operational. Not every team wants every model touching their telemetry, so TierZero supports LLM model restrictions. A customer can restrict the agent to Gemini and Claude, or whatever subset their security team has reviewed, and the restriction is respected at every reasoning step. And for regulated environments, cloud-only is a non-starter. TierZero deploys fully on-premises via Terraform on AWS or GCP, the entire system runs inside the customer's environment with only billing and usage data leaving, zero-data-retention is configurable, SOC 2 Type II certified, HIPAA compliant.
The general principle here is uncomplicated: a security agent has to clear the same bar as the things it's monitoring. Anything less is a new attack surface dressed up as a defense.
How TierZero Handles This Specifically
Three pieces of the platform do most of the work for cloud security, and they compose. The Proactive Discovery agent is the continuous reasoning layer that watches infrastructure, deploys, configuration, and runtime telemetry and surfaces drift, dependency exposure, capacity risk, schema mismatches, and silent failure modes. It runs without being asked. The Context Engine is the shared knowledge layer underneath every agent: service topology, deploy history, alert patterns, ownership, runbooks. It's what turns "here is a CVE in your dependency tree" into "here is the one service in your environment that is actually exposed, here is who owns it, here is the patch path." The Memory Explorer is where the auditability shows up. Every claim the agent makes is grounded in something specific: a deploy event, a config change, a historical incident, a piece of documentation. The Explorer surfaces that evidence chain and lets your team correct the record when the agent is wrong, with the agent learning from the correction without retraining.
Together, those three components turn cloud security from a periodic audit into a continuous, reasoning-driven workflow. The agent watches and surfaces what matters with the receipts attached. The team decides what to do with it.
The Bigger Picture
Cloud security used to be a moment-in-time discipline. Run the scan, file the findings, patch the queue, repeat next quarter. That model worked when the average engineering org ran a handful of services. It broke when the average org started running fifty, then five hundred. Once the surface area outran the team, snapshot-based security stopped being a real defense and turned into a compliance ritual.
Continuous reasoning is the architecture that scales with what infrastructure has actually become. You can't scan your way to safety when the environment changes hundreds of times a day. You need an agent that lives inside the change stream, watching, correlating, and surfacing exposures that matter before they pile up.
The teams getting this right aren't the ones with the biggest security budgets. They're the ones who reframed the problem. Security stopped being a periodic audit and became a continuous reasoning problem. AI is the only viable architecture for that work, and TierZero was built by operators from Meta, Databricks, and Niantic to handle exactly this shift: production AI agents that watch the surface area no human team can hold in their head.
The decision in front of most engineering leaders today isn't whether to add AI to their cloud security stack. It's whether the agent they pick reasons across signals or just runs rules faster.
See Proactive Discovery in Action
Book a TierZero demo. We'll show you what continuous reasoning looks like on real infrastructure, and how the Proactive Discovery agent catches risks before they page anyone.
Co-Founder & CEO at TierZero AI
Previously Director of Engineering at Niantic. CTO of Mayhem.gg (acq. Niantic). Owned social infrastructure for 50M+ daily players. Tech Lead for Meta Business Manager.
LinkedIn